Security & Permission Systems
Frameworks control access to systems and data across overlapping teams, tools, and projects.
Linux systems
A hierarchical, permissioned operating system manages processes, memory, and files through a kernel that enforces resource isolation, scheduling, and hardware abstraction.

A hierarchical, permissioned operating system manages processes, memory, and files through a kernel that enforces resource isolation, scheduling, and hardware abstraction.
This domain is valuable because software and platform systems make interfaces explicit. They reveal how modules compose, where abstractions leak, how change propagates, and how operational discipline keeps complex systems evolvable.
The same lens transfers far beyond software. Once you can reason about state, isolation, coordination, and failure here, you are better prepared to understand teams, institutions, and other layered systems. This domain gets more useful when it is compared with adjacent systems instead of being treated as a silo. That is where reusable judgment starts to form.
Frameworks control access to systems and data across overlapping teams, tools, and projects.

Experimented with iBeacon transmitters placed around the house to track room-by-room location before indoor positioning was a product category.
Persistence layers provide durability, availability, and performance through replication, partitioning, and tiering.

Projects building and operating personal infrastructure — servers, clusters, networks, and the experiments that run on them.
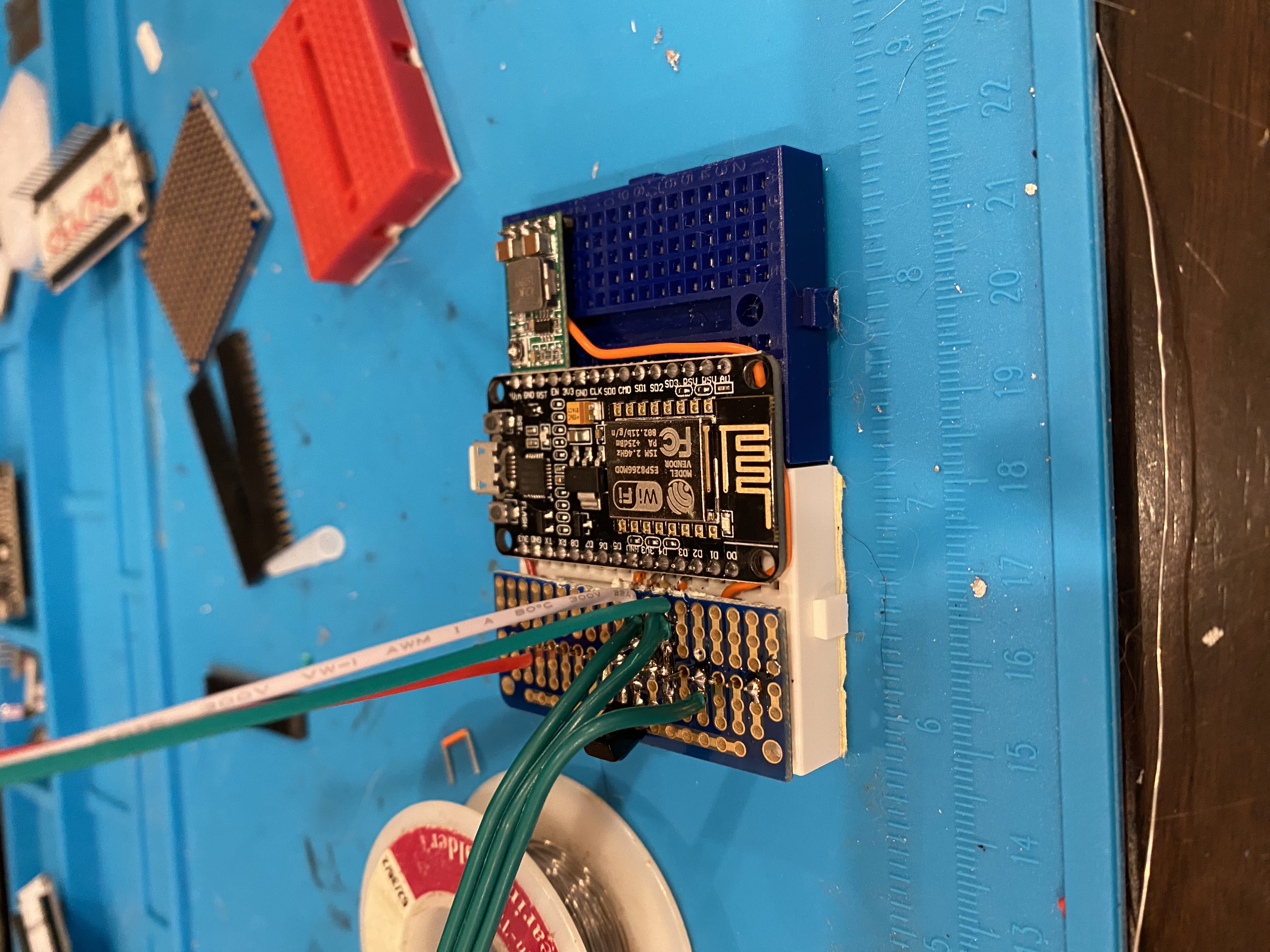
A proof of concept using ESP8266 microcontrollers to demonstrate that rotating MAC addresses can still be fingerprinted via broadcast SSIDs.